Google’s Risk Intelligence Group (GTIG) is warning {that a} “new and highly effective” iOS exploit package, dubbed Coruna by its builders has been deployed on faux finance and crypto web sites designed to lure iPhone customers into visiting pages that may silently ship exploits. For crypto holders, the chance is blunt: GTIG’s evaluation reveals the campaigns in the end targeted on harvesting seed phrases and pockets information from common cellular apps.
Coruna targets Apple gadgets operating iOS 13.0 via iOS 17.2.1, bundling 5 full exploit chains and 23 exploits. GTIG says it recovered the package after monitoring its evolution throughout 2025, from early use by a buyer of a business surveillance firm, to “watering gap” assaults on compromised Ukrainian web sites, and eventually to broad-scale distribution by way of Chinese language-language rip-off websites tied to a financially motivated actor it tracks as UNC6691.
A Crypto Lure Designed For iPhones
Within the scam-wave part, GTIG says it noticed the JavaScript framework behind Coruna deployed throughout a “very giant set” of pretend Chinese language web sites largely themed round finance. One instance cited by GTIG is a faux WEEX-branded crypto alternate web page that attempted to push guests onto an iOS machine—after which a hidden iFrame can be injected to ship the exploit package “no matter their geolocation.”
Associated Studying
The supply mechanics matter as a result of they blur the road between conventional phishing and outright machine compromise: in GTIG’s telling, merely arriving on the booby-trapped web page from a susceptible iPhone was sufficient to start the chain. The framework fingerprints the machine to establish mannequin and iOS model, then masses the suitable WebKit distant code execution exploit and a pointer authentication (PAC) bypass.
GTIG tied one WebKit RCE it recovered to CVE-2024-23222, noting it was addressed by Apple in iOS 17.3 on Jan. 22, 2024.
On the finish of the chain, GTIG says Coruna drops a stager it calls PlasmaLoader (tracked as PLASMAGRID) and describes it as targeted much less on basic surveillance options and extra on stealing monetary data. In response to GTIG, the payload can decode QR codes from photographs saved on the machine and scan textual content blobs for BIP39 phrase sequences, together with key phrases corresponding to “backup phrase” and “checking account”, together with in Apple Memos, which it might probably then exfiltrate.
Associated Studying
The payload can also be modular. GTIG says it might probably pull down and run extra modules remotely, and that most of the recognized modules are designed to hook capabilities and exfiltrate delicate data from frequent crypto pockets apps—amongst them MetaMask, Belief Pockets, Uniswap’s pockets, Phantom, Exodus, and TON ecosystem wallets corresponding to Tonkeeper.
The broader arc was additionally flagged by cellular safety agency iVerify, which printed its personal findings across the identical time as GTIG’s report. “And that’s precisely what occurred once more right here, however on cellular gadgets. Cellphone OEMs do nearly as good a job as anybody can do…”
What Crypto Customers Can Do Now
Google says Coruna “just isn’t efficient in opposition to the newest model of iOS,” and urges customers to replace. If updating isn’t attainable, GTIG recommends enabling Apple’s Lockdown Mode. GTIG additionally says it added the recognized web sites and domains to Google Secure Shopping to assist scale back additional publicity.
For crypto-native customers, the quick takeaway is sensible: cellular wallets sit on the intersection of high-value belongings and high-frequency net site visitors, which makes “visit-to-compromise” campaigns uniquely harmful. GTIG’s reporting suggests the rip-off funnel wasn’t nearly getting victims to attach wallets, it was about getting them onto the suitable machine, on the suitable iOS model, so exploitation might do the remainder.
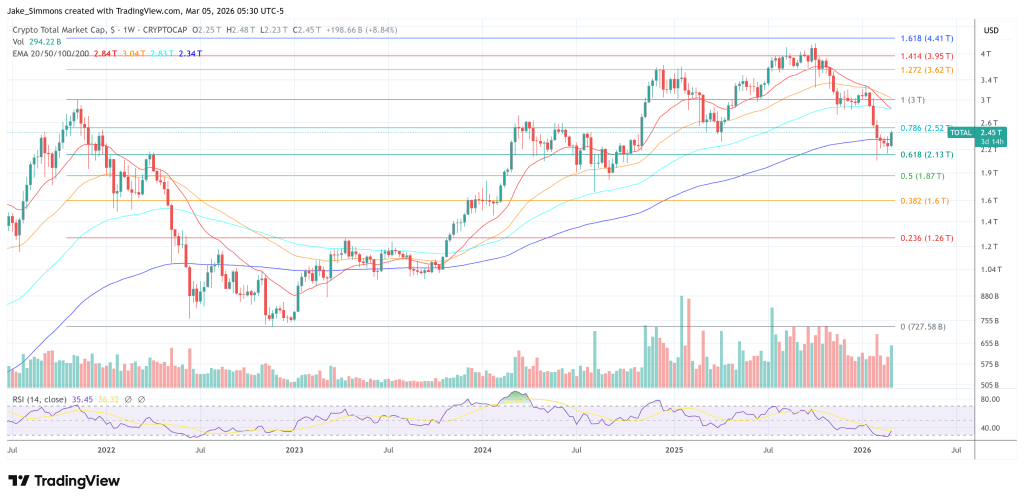
At press time, the overall crypto market cap stood at $2.45 trillion.
Featured picture created with DALL.E, chart from TradingView.com
