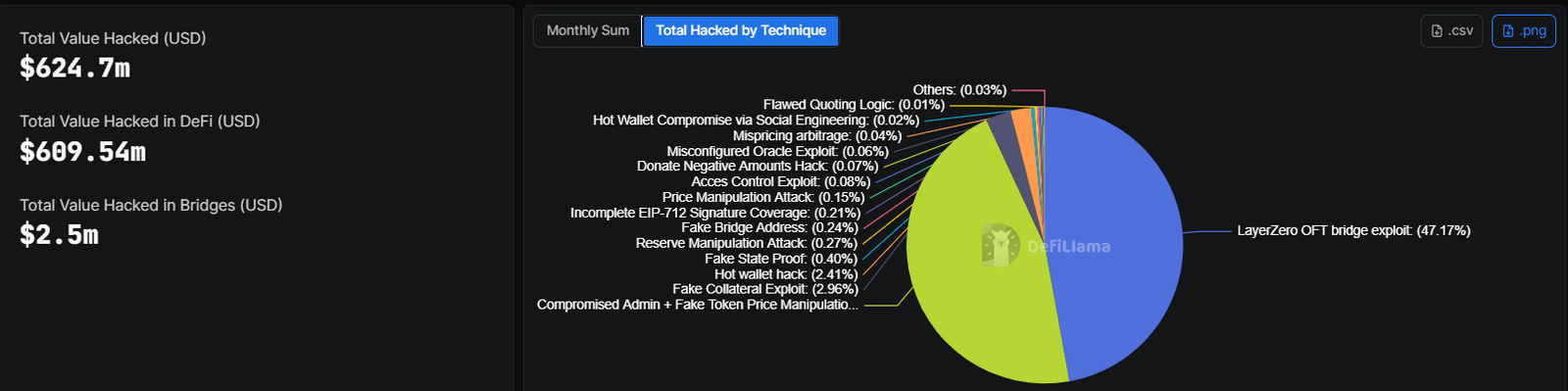
Bridge exploits and admin compromises drove most April losses, exposing vital weaknesses in DeFi infrastructure layers.
April 2026 marked a pointy escalation in crypto safety breaches, with losses reaching $620 million throughout simply 20 days. Exercise spanned 12 separate incidents, making it the worst month for the reason that Bybit breach in February 2025. Assault patterns ranged from social engineering to sensible contract failures, with no single technique dominating early on. Nonetheless, knowledge reveals a transparent clustering of losses round just a few vital weaknesses.
Complete damages have been 3.7 instances larger than the mixed whole for all of Q1 2026. A good portion of losses got here from infrastructure-level vulnerabilities slightly than remoted coding errors. Cross-chain bridges, admin entry factors, and collateral programs turned major targets. Attackers targeted on areas the place belief and automation intersect.
Early Crypto Hack Wave Pushed by Social Engineering
In line with DefiLlama, April opened with one of many largest incidents of the 12 months. Drift Protocol suffered a $285 million exploit tied to long-term social engineering. Attackers spent months posing as a buying and selling agency to construct credibility with inner groups.
Picture Supply: DefiLlama
Entry got here by means of pre-signed transactions accepted by Safety Council members. As soon as management was gained, attackers deposited faux collateral and drained vaults inside minutes. Experiences linked the breach to North Korean hacking teams, including geopolitical weight to the incident.
Smaller exploits adopted shortly, as Silo Finance misplaced $392,000 on account of an oracle misconfiguration. On the identical day, Dango suffered a $410,000 loss tied to a sensible contract bug. Each instances pointed to ongoing dangers in protocol setup and auditing practices.
Stress on liquidity swimming pools elevated after a $1.67 million exploit focusing on BSC buying and selling pairs. A flash mortgage assault on the BNB Chain adopted, draining $1.6 million by manipulating reserves.
- Social engineering enabled deep system entry with out code-level exploits
- Oracle misconfigurations uncovered lending protocols to pricing errors
- Flash loans allowed fast reserve manipulation in low-liquidity swimming pools
- Good contract bugs remained a recurring however smaller contributor
Aethir misplaced $423,000, whereas SubQuery Community and Hyperbridge recorded mixed losses exceeding $2.5 million. Assault surfaces expanded past core DeFi into infrastructure layers.
Area hijacking added one other dimension. CoW Swap misplaced $1.2 million after attackers took management of its area. Zerion additionally reported a $100,000 exploit, displaying frontend programs stay weak.
Mid-Month Escalation Hits Exchanges and Lending
Mid-April noticed a shift towards bigger coordinated breaches. Grinex misplaced $13.74 million, with funds routed throughout dozens of wallets. The platform attributed the assault to international intelligence actors, although verification stays unclear.
On the identical time, Rhea Lend recorded an $18.4 million exploit. Transaction evaluation by Chainalysis steered a doable exit rip-off, leaving uncertainty round intent.
Consideration then shifted to cross-chain infrastructure. Kelp DAO suffered a $292 million exploit tied to a LayerZero bridge vulnerability. Attackers drained 116,500 rsETH in a single transaction, equal to 18% of the availability.
Influence unfold shortly throughout DeFi lending markets. Aave now faces $177 million in unhealthy debt linked to unliquidatable rsETH collateral. Credit score threat has elevated for one of many sector’s largest platforms.
Bridge-related exploits accounted for 47.17% of whole losses through the month. Different strategies remained fragmented, with every contributing lower than 3% individually.
Late-Month Crypto Hack Exercise Reveals Systemic Weak spot
Later incidents confirmed that vulnerabilities weren’t remoted. Juicebox and Thetanuts Finance misplaced modest quantities, whereas Volo Vault recorded a $3.5 million breach tied to vault design.
Additional exploits hit Kipseli and Giddy, displaying attackers continued focusing on smaller platforms. Earlier losses from MONA added to the cumulative impression.
- Pretend collateral exploits accounted for practically 3% of whole losses
- Pretend state proof assaults uncovered weaknesses in verification programs
- Reserve manipulation confirmed continued threat in automated market makers
- Signature validation gaps allowed unauthorized transaction approvals
Weekend exercise added one other case to the latest hacks. Purrlend misplaced $1.5 million after a suspicious multisig transaction granted unauthorized bridge entry. Attackers exploited the brand new privileges inside hours.
Cross-chain bridges stay a constant level of failure. April’s knowledge confirms {that a} small set of weaknesses drove most losses. Admin entry, bridge infrastructure, and collateral programs carried the best threat focus.
Crypto safety strain continues to construct as attackers refine strategies throughout each on-chain and off-chain vectors.