- Polygon, Ledger, Trezor break silence on yesterday’s NPM hack
- Largest JavaScript NPM hack: What you must know
To this point, no cryptocurrency service has reported losses on account of clipper malware being injected into NPM packages, inevitable devices for JavaScript builders. On the similar time, cryptocurrency customers ought to keep notably vigilant lately.
Polygon, Ledger, Trezor break silence on yesterday’s NPM hack
In keeping with official statements by cryptocurrency groups, increasingly more companies have confirmed that their tech architectures are unaffected by the Sept. 8 NPM assault, the largest hack within the historical past of JavaScript.
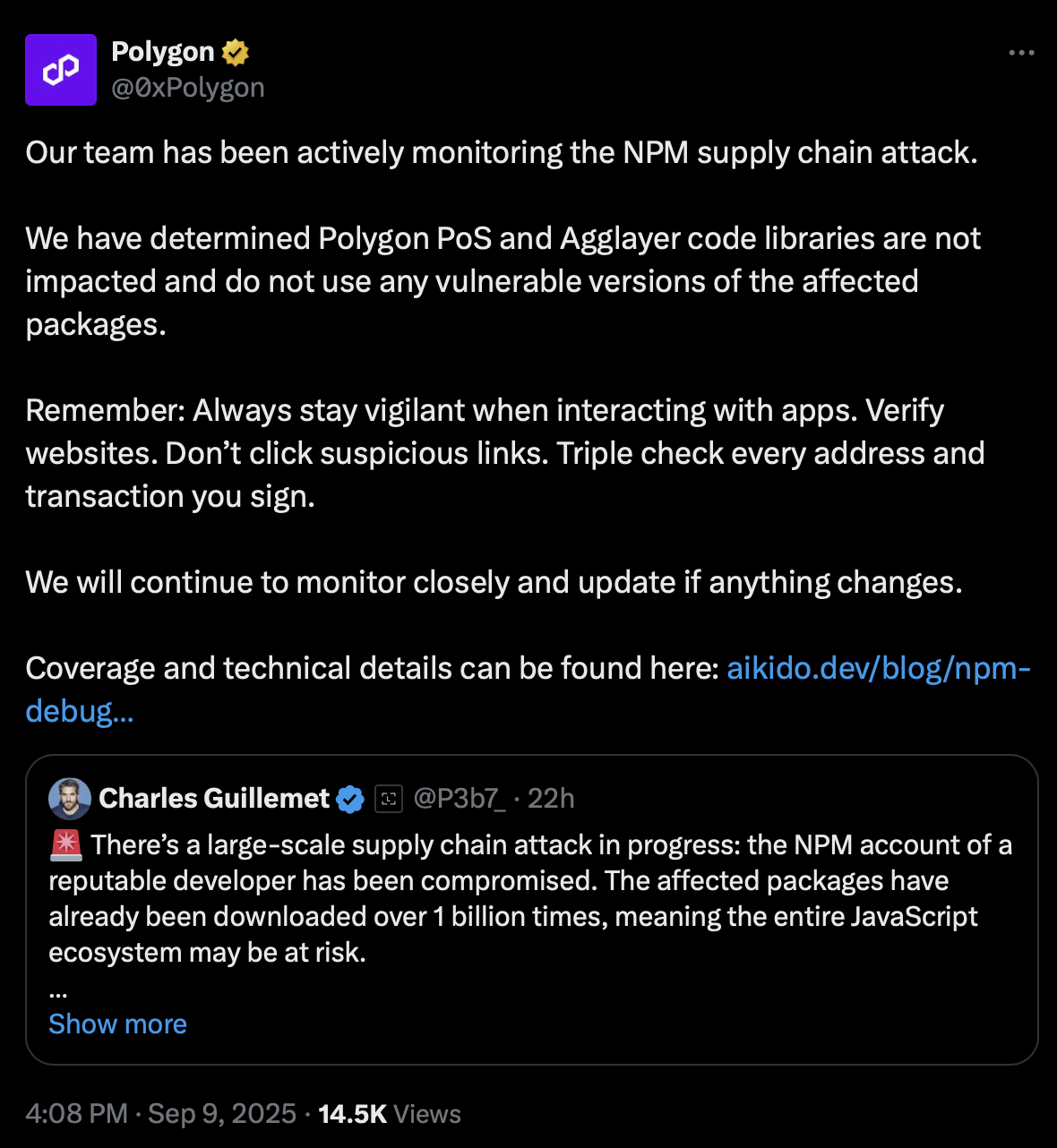
Polygon (POL), the biggest layer-2 blockchain on Ethereum Digital Machine, assured readers that each Polygon Proof-of-Stake and Agglayer are unaffected by the collapse.
Most significantly, comparable statements have been launched by the cryptocurrency pockets’s workforce. {Hardware} pockets producer Ledger, whose CTO Charles Guillemet knowledgeable the crypto area concerning the hack, confused that every one funds are secure.
Ledger units should not and haven’t been in danger throughout an ecosystem-wide software program provide chain assault that was found. Ledger units are constructed particularly to guard customers in opposition to assaults like these.
Trezor, one other top-tier supplier of {hardware} cryptocurrency wallets, outlined that at no stage have been the devices uncovered to the attackers.
Trezor Suite, an app crucial to attach Trezor wallets to computer systems, can be secure, the assertion says.
Largest JavaScript NPM hack: What you must know
Yesterday, on Sept. 8, 2025, the account of a good JavaScript software program developer was hacked. The malefactors uploaded tampered NPM packages — parts of JS code — infiltrated with the malware concentrating on crypto on all main blockchains.
Altered NPM packages could be downloaded billions of instances as JS is without doubt one of the dominant programming languages proper now.
Clipper malware replaces the handle a sufferer sends crypto to with the handle of the hacker. Because of this, the person sends cash to the attacker with out figuring out it.
All crypto customers ought to be tremendous cautious lately whereas sending funds on-chain and when signing approvals through Web3 wallets.